Published articles
82 articles-

Latest Interesting Cybersecurity News - 2026-04-05
Latest interesting cybersecurity news from May 2026
-
Access That Follows Responsibility, Not Org Charts
Most platforms manage access by restricting it. Kordon does the opposite — access is earned by assignment and revoked the moment that assignment ends. No legacy visibility, no periodic cleanups.
-
Why Business Process Management Is the Missing Link in GRC
Most GRC programs are built around frameworks and controls, not around the business itself. Learn why connecting your assets, risks, and vendors to business processes is what makes security management actually work.
-
Latest Interesting Cybersecurity News - 2026-26-04
Latest interesting cybersecurity news from April 2026
-
Latest Interesting Cybersecurity News - 2026-20-04
Latest interesting cybersecurity news from April 2026
-

Latest Interesting Cybersecurity News - 2026-13-04
Latest Interesting Cybersecurity News summary for 13 April 2026.
-
Latest Interesting Cybersecurity News - 2026-06-04
Latest interesting cybersecurity news from April 2026
-

Latest Interesting Cybersecurity News - 2026-03-30
Latest interesting cybersecurity news from March 2026
-
Latest Interesting Cybersecurity News - 23-03-2026
Latest interesting cybersecurity news from March 2026
-
Latest Interesting Cybersecurity News - 16-03-2026
Latest interesting cybersecurity news from March 2026
-
Latest Interesting Cybersecurity News - 09-03-2026
Latest interesting cybersecurity news from March 2026
-

Latest Interesting Cybersecurity News - 01-03-2026
Latest interesting cybersecurity news from March 2026
-
Latest Interesting Cybersecurity News - 23-02-2026
Latest interesting cybersecurity news from February 2026
-
Latest Interesting Cybersecurity News of the Week Summarised - 16-02-2026
Latest interesting cybersecurity news from February 2026
-
Latest Interesting Cybersecurity News of the Week Summarised - 09-02-2026
Latest interesting cybersecurity news from February 2026
-
Latest Interesting Cybersecurity News of the Week Summarised - 02-02-2026
Most interesting cybersecurity news from last week of January 2026.
-
Cybersecurity News Worth Your Attention this Week Summarised - 26-01-2026
Here are the latest cybersecurity stories from January 2026: I go through about 25 cybersecurity news portals and blogs every week and pull out the most...
-
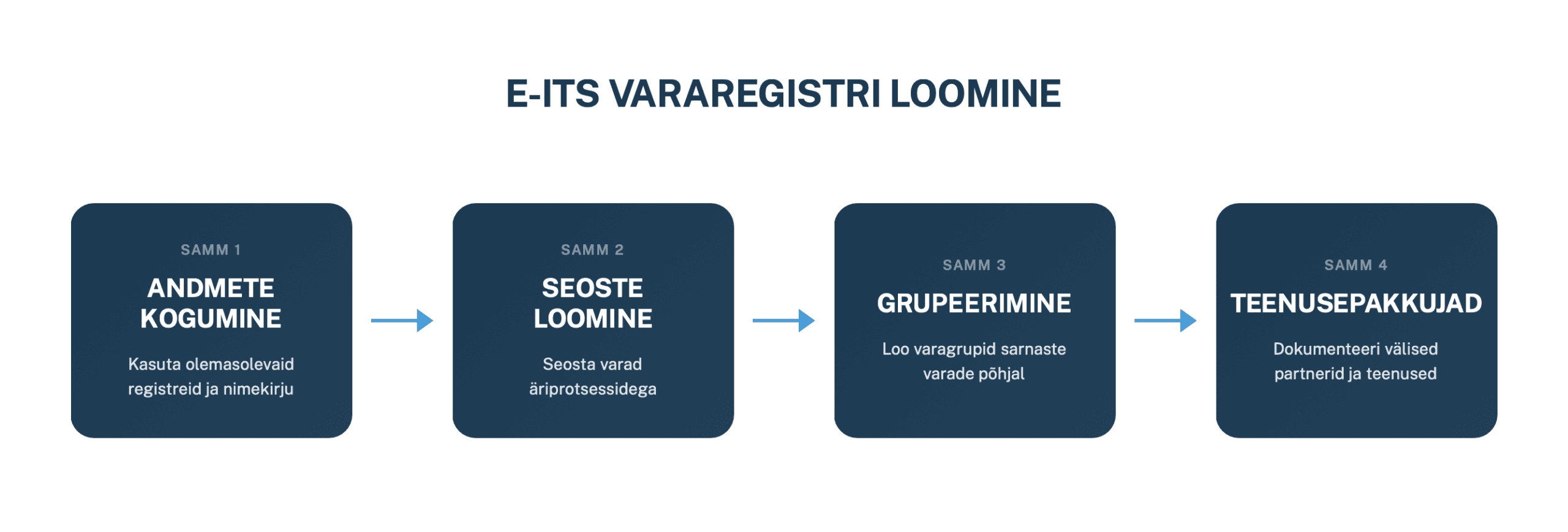
Detailne juhend: Kuidas luua E-ITS varade ja teenusepakkujate register
Praktiline juhend, kuidas kaardistada E-ITS või ISO 27001 rakendamisel varasid ja teenusepakkujaid ning luua registrid, mis toetavad päriselt riskijuhtimist ja kaitsemeetmete valikut.
-
Latest Interesting Cybersecurity News of the Week Summarised - 19-01-2026
I go through about 25 cybersecurity news portals and blogs every week and pull out the most interesting stories. Then I turn them into this short, diges...
-
This Week in Cybersecurity News - 12-01-2026
Latest Cybersecurity News Summary from January 2026.
-
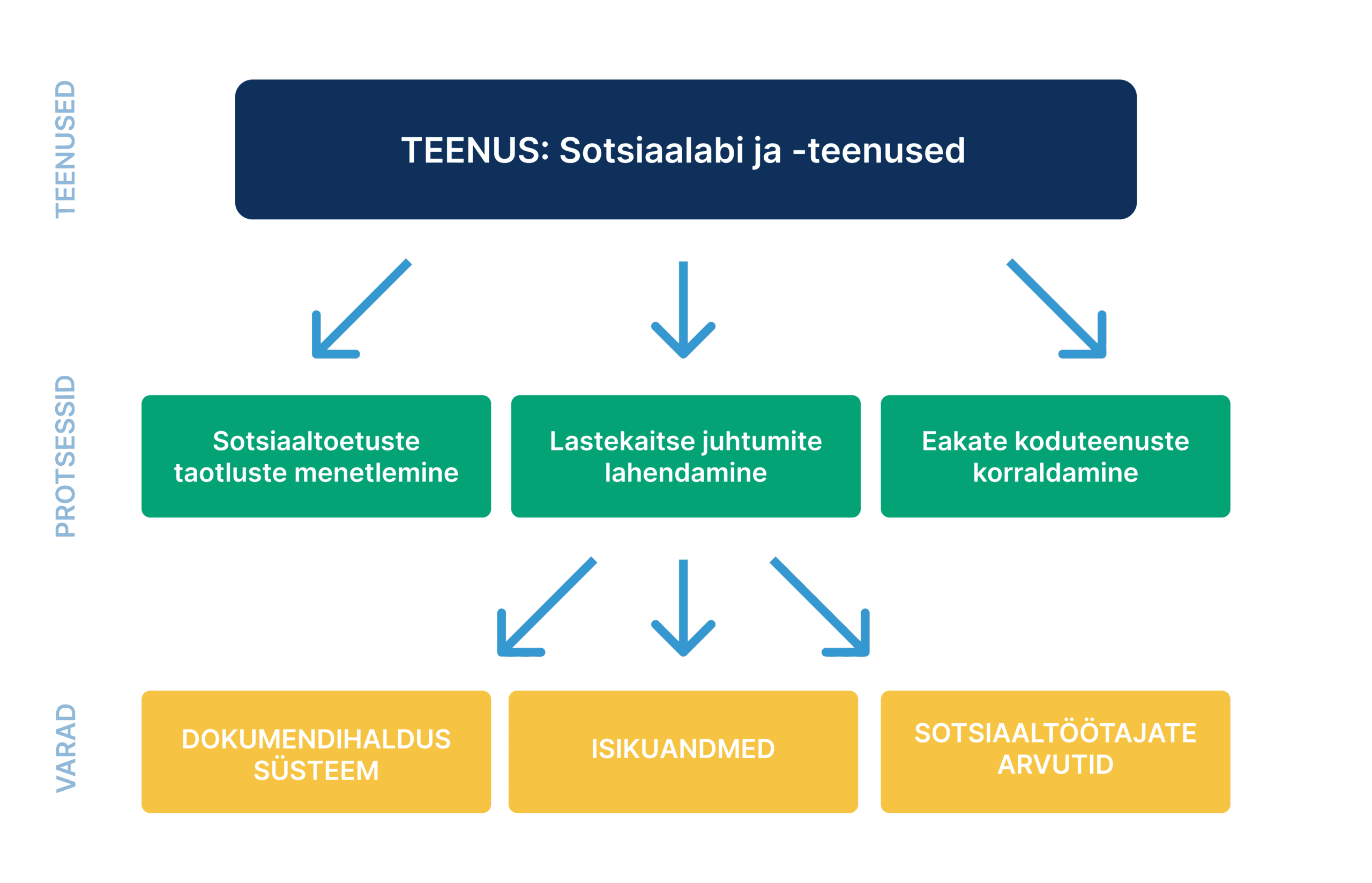
Detailne juhend: Kuidas määratleda E-ITS äriprotsesse?
E-ITS äriprotsesside kaardistamine ja määratlemine: praktiline samm-sammult juhend. Õpi, kuidas dokumenteerida äriprotsesse ja alustada infoturbejuhtimist.
-
Latest Interesting Cybersecurity News of the Week Summarised - 05-01-2026
Latest interesting cybersecurity news roundup from January 2026.
-
Latest Interesting Cybersecurity News of the Week Summarised - 29-12-2025
Latest Cybersecurity news from December 2025. I go through about 25 cybersecurity news portals and blogs every week and pull out the most interesting st...
-

Interesting Cybersecurity News of the Week Summarised - 22-12-2025
I go through about 25 cybersecurity news portals and blogs every week and pull out the most interesting stories. Then I turn them into this short, diges...
-
Interesting Cybersecurity News of the Week Summarised - 15-12-2025
I go through about 25 cybersecurity news portals and blogs every week and pull out the most interesting stories. Then I turn them into this short, diges...
-
Interesting Cybersecurity News of the Week Summarised - 07-12-2025
I go through about 25 cybersecurity news portals and blogs every week and pull out the most interesting stories. Then I turn them into this short, diges...
-
Interesting Cybersecurity News of the Week Summarised - 01/12/2025
I go through about 25 cybersecurity news portals and blogs every week and pull out the most interesting stories. Then I turn them into this short, diges...
-

Interesting Cybersecurity News of the Week Summarised - 2025-11-24
This week two topics stayed with me after putting this summary together. First, when did I last update my home router, because routers getting breached...
-

Interesting Cybersecurity News of the Week Summarised - 2025-17-11
Latest Interesting Cybersecurity News from November 2025.
-

Interesting Cybersecurity News of the Week Summarised - 2025-11-10
Latest interesting cybersecurity news from November 2025.
-
Interesting Cybersecurity News of the Week Summarised - 2025-11-03
Latest interesting cybersecurity news from the last week of October 2025.
-

Cybersecurity News Worth Your Attention this Week Summarised - 2025-10-27
Summary of latest cybersecurity news from October 2025.
-
Cybersecurity News Worth Your Attention This Week- 2025-10-20
Summary of latest cybersecurity news from October 2025.
-
Cybersecurity News Worth Your Attention This Week - 2025-10-06
Weekly summary of latest cybersecurity news in October 2025.
-
Summaries of Cybersecurity News Worth Your Attention this Week - 2025-05-10
Summaries of cybersecurity news from first week of October 2025.
-
Summaries of Cybersecurity News Worth Your Attention this Week - 2025-09-29
New technologies are awesome, they often allow us to achieve more, get further, be more creative. But unfortunately, this is true for the bad guys as we...
-
Summaries of Cybersecurity News Worth Your Attention this Week - 2025-09-22
From this weeks cybersecurity news summary we learn that cyberattacks definitely impact our every day lives – like yesterday when quite a few airports i...
-
Cybersecurity News Worth Your Attention This Week Summarised - 2025-09-15
This week summary of latest cybersecurity news from September 2025 feels like a greatest hits album of “what could possibly go wrong.” We’ve got npm pac...
-
Cybersecurity News Worth Your Attention This Week Summarised - 2025-09-08
The anti-hero of the week is a classic Word marco that was used to spear phish 50 embassies, ministries and international organisations. We also have th...
-
8 Cybersecurity News Worth Your Attention this Week Summarised - 2025-09-01
8 Latest cybersecurity news from last week of August 2025.
-

12 Cybersecurity News Worth Your Attention this Week Summarised - 2025-08-25
12 Latest cybersecurity news from 25th of August 2025.
-

11 Cybersecurity News Worth Your Attention this Week Summarised -18/08/2025
Summary of Latest cybersecurity news in August 2025.
-

11 Cybersecurity News Worth Your Attention this Week Summarised -11/08/2025
Summary of Latest cybersecurity news first week of August 2025.
-
17 Cybersecurity News Worth Your Attention this Week Summarised - 04/08/2025
Summary of Latest cybersecurity news August 2025.
-
14 Cybersecurity News Worth Your Attention This Week Summarised - 28/07/2025
Latest interesting and actionable cybersecurity news summarised from the last week of July 2025.
-
18 Cybersecurity News Summarised - 21/07/2025
Most interesting and actionable cybersecurity news summarised from the 3rd week of July 2025. Theme of the week is definitely Asia, lot’s of activity fr...
-

317 Example Vendors for ISO 27001, NIS 2, and DORA Compliance (Free CSV Template Download)
Free / no signup CSV download of 317 common vendors documented and categorised by business process. Suitable for ISO 27001, SOC2, NIS2, DORA etc.
-

13 Cybersecurity News Summarised - 14/07/2025
Most interesting and actionable cybersecurity news summarised from the 2dn week of July 2025. I got to say, this week was a busy one for the criminals....
-

Top Cybsersecurity News Summarised - 1st Week of July 2025
Most interesting and actionable cybersecurity news summarised from the 1st week of July 2025.
-

9 Cybersecurity News from This Week Worth Your Attention (June 2025)
9 actionable and interesting cybersecurity news from the last week of June 2025 summaries.
-

16 Cyber Security News from June Worth Your Attention
We scan more than 20+ cybersecurity news sites every week to highlight only the stories that truly matter.
-
13 Cybersecurity News Worth Your Attention - 1st Week of June 2025
Summaries of top cybersecurity news from 3rd week of May
-

10 Cybersecurity News You Should Know From 3rd Week of May 2025
Summaries of top cybersecurity news from 3rd week of May
-
No Warrant, No Problem: How Governments Are Building the Surveillance Super App
The U.S. Government is building a super app to monitor everyone without warrants. Where are they getting the data from and how can we protect ourselves?
-

Vendor Tiering in Practice: How to Calibrate Vendor Levels Without Overkill
This post is about making vendor tiering meaningful, so that each tier reflects the vendor’s real exposure and operational importance and efforts can be scaled accordingly.
-

13 Cybersecurity News Worth Your Attention This Week (2/4 May 2025)
Quick summaries of cybersecurity news from May 2025 worth your attention.
-
How to Build a Vendor Risk Management Framework
A practical guide to the core pieces of a vendor risk management framework and how to shape them into a repeatable, auditable process.
-
18 Cyber Security News Worth Your Attention in First Week of May
Fourth week in a row, I spent hours going throguh 20+ different cyber security news sources to find most interesting articles from last week so you can...
-
Vendor Management vs. Vendor Risk Management: What's the Difference?
Clearly defining the difference between vendor management and vendor risk management helps you assign ownership correctly and avoid gaps as your organisation grows.
-
14 Cyber Security News Worth Your Attention from Last Week of April
I spent a few hours reviewing 17 cyber security news portals, handpicking the most interesting cyber securityu news from the last week of April and summ...
-
17 Cyber Security News Worth Your Attention This Week
Weekly roundup: 17 must-read cybersecurity stories for April 2025: ransomware franchise models, CVE funding drama, Chrome IP Protection, OT sabotage & more
-
On-Premises GRC Platform: Pros, Cons, and When It Makes Sense
Explore the practical pros and cons of choosing an on-premises GRC platform instead of a vendor-hosted cloud deployment.
-
How an Attacker Used 'Spam Bombing' to Gain Remote Access
A short breakdown of how spam bombing can be used in social engineering and what teams can do to spot and resist it.
-
Security News Roundup From Last Week That We Found Interesting - 14 April 2025
A concise cybersecurity news roundup for 14 April 2025 covering Perplexity's Android app flaws, spam bombing in social engineering, the IKEA operator ransomware fallout, and Google's Sec-Gemini v1 announcement.
-
You're an InfoSec Professional Not a Kinderkarten Teacher
Every minute you spend chasing other people for security work is a minute stolen from actual security work.
-
How To Do Policy Training Better
Because nobody learns from a snoozefest. List of actionable small adjustments to make your trainings less boring.
-
19 Essential KPIs to Track Your ISMS's Effectiveness
List of universal KPIs and metrics to measure the progress and effectiveness of any information security management program.
-
GRC Metrics & KPIs Checklist with Example KPIs
A practical checklist for choosing GRC KPIs that support risk reduction, compliance progress, and measurable improvement over time.
-

Risk Management Fail: Mixing Causes with the Risk Itself
People often mix up the risk itself with its potential cause or mitigation. This mistake can significantly impact how risks are understood and managed.
-

NIS 2 Just Came Out But We Already Know What NIS 3 Will Bring
NIS 2 is already shifting expectations for smaller organizations. Based on current regulatory and resilience trends, we can already see what a likely NIS 3 direction would demand from SMBs.
-
The Highest Vendor Risk Happens AFTER Onboarding: Vendor Drift
Vendor risk does not stop at onboarding. This post explains vendor drift, the signals to watch for, and how to monitor third-party risk over time.
-
Choosing the Right Risk Matrix: Hidden Biases and How to Overcome Them
Overview of hidden biases in risk scoring and practical ways to overcome them.
-
Is “We Don’t Use Your Data for AI Training” Enough?
What other ways besides training could your data be used by an AI provider and how to mitigate risks that come with that.
-
How to Collaborate within the Organisation to Capture All Assets?
Learn how to collaborate across teams, engage key stakeholders, and streamline asset discovery for a complete inventory. Simple, effective, and practical tips!
-
How to Guide: Mapping Assets to Business Processes
Map assets to business processes to improve security, manage risks, and prioritize protection. Learn how to uncover dependencies and avoid common pitfalls.
-
How to Choose a Risk Management Tool?
This article explores key tools to manage risk and criteria to choose the best ones for your organization.
-
The Ultimate Guide to Asset Inventory Management
Ultimate guide on asset inventory management focusing on practical steps you can take to move beyond basic inventory tracking, using modern tools, processes, and collaboration to turn asset management into a strategic asset that continuously supports security, compliance, and operational resilience.
-
Top Information Security Risks to monitor in 2025
Explore the top 10 information security risks for 2025, featuring real-world examples of each threat.
-
25 Essential Operational Risks with Practical examples
Practical real world examples of operational risks for every modern organisation to consider. Includes downloadable example risk registry CSV.
-
5 categories of risk modern companies need to consider
A deep dive into different categories of risk a modern company needs to consider, with real world examples.
-
Asset Inventory Best Practices to Build Resilience and Security
A solid asset inventory is key to meeting ISO 27001 requirements and strengthening your security management. In this article, we’ll cover practical tips for building and maintaining an asset inventory that keeps your compliance on track and your security robust. Get ready for actionable steps you can implement right away.
-
ISO 27001 Asset Inventory Example: A Complete List of 140 Assets + Free CSV
Free downloadable list of 140 assets—including IT systems, data, and infrastructure—to help you build a complete inventory and level up your asset management system.









