In 7 to 8 years, many non-technical organizations, including traditional family businesses, will likely need a formal information security program.
That sounds bold, but the direction is visible already.
Why this matters right now
NIS 2 has only recently moved into active implementation, yet it has already changed expectations around governance, accountability, and evidence. In parallel, ecosystem risk keeps rising through third-party dependencies.
The key question is no longer whether stricter baseline requirements will spread to smaller organizations.
The key question is when.
What changed between 2022 and 2025
The World Economic Forum Global Cybersecurity Outlook highlights two directional signals:
- Confidence in cyber regulation as an effective resilience mechanism increased significantly.
- Smaller organizations reported worsening resilience outcomes compared with larger organizations.

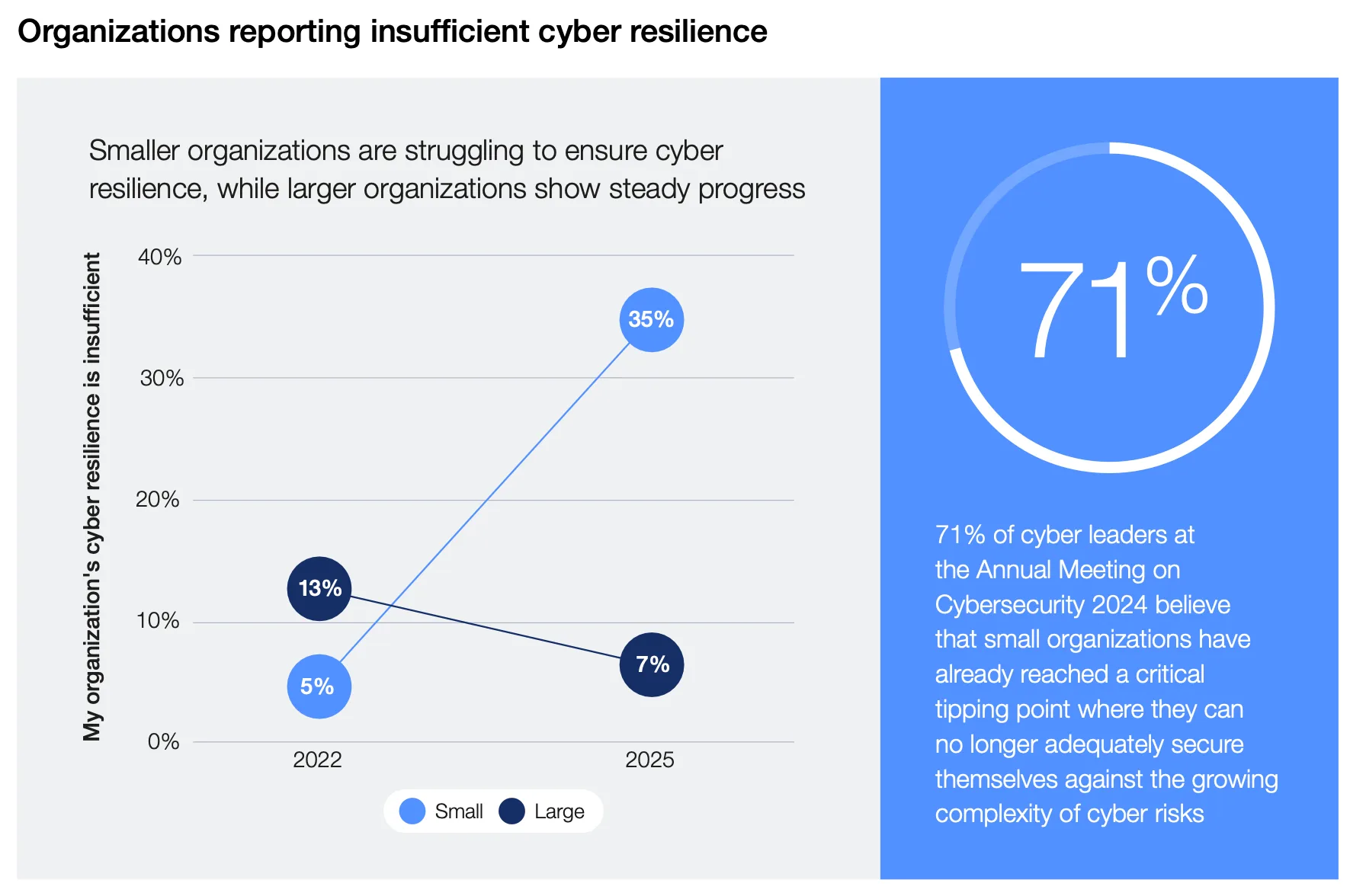
When those two trends run in parallel, policymakers and large enterprises get the same incentive: raise the baseline for the weakest links in the chain.
Why NIS 3 is predictable even before it is written
A likely NIS 3 direction does not require guessing specific legal text. We only need to follow the incentives:
- Critical services and large enterprises depend on suppliers.
- Supplier ecosystems include many small organizations.
- Systemic resilience fails when those suppliers cannot meet minimum governance and control expectations.
That creates pressure to expand practical security obligations beyond the organizations currently in strict scope.
If ecosystem resilience is the policy goal, broadening expectations for smaller organizations becomes a structural outcome, not a surprise.
What this means for SMBs
If you run a smaller organization, waiting for explicit legal inclusion is usually the most expensive strategy.
A better approach is to establish a lightweight but real GRC baseline now:
- Build and maintain a risk register tied to actual assets and business processes.
- Define control ownership so every critical control has a person responsible.
- Track evidence continuously, not once a year before an audit.
- Keep supplier risk reviews proportionate but repeatable.
- Make your Statement of Applicability and policy decisions traceable.
These are not enterprise-only practices anymore. They are quickly becoming default operating hygiene.
A practical next step
Pick one core process this month and make it auditable end to end. For example:
- Vendor onboarding
- Access review
- Incident logging and closure
Then turn that single process into a recurring cycle with ownership, due dates, and evidence. That gives you momentum without trying to implement everything at once.
